- Nicholas Moore pleaded guilty to repeatedly hacking the US Supreme Court’s electronic filing system.
- New court filings say he also accessed AmeriCorps and Department of Veterans Affairs systems.
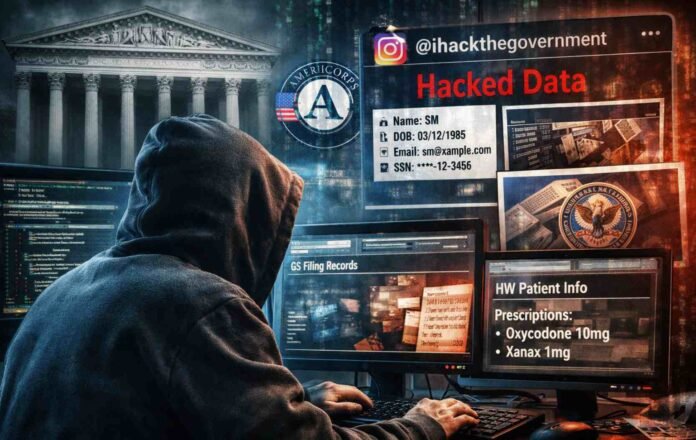
- He allegedly used stolen credentials and posted victims’ personal data to Instagram.
- He faces up to one year in prison and a $100,000 maximum fine.
A 24 year old Tennessee man who admitted breaking into the US Supreme Court’s electronic filing system also allegedly stole personal data from other federal networks and then posted parts of it publicly on Instagram, according to newly filed court documents.
The hacker, Nicholas Moore of Springfield, Tennessee, pleaded guilty last week to repeatedly accessing the Supreme Court’s electronic document filing platform. At the time, the plea did not reveal much beyond the fact that the system had been targeted. Now, a fresh filing has filled in the missing pieces, showing a broader pattern of intrusions and a troubling motive that went beyond simple curiosity or a private thrill.
Investigators say Moore used stolen login credentials belonging to legitimate users who were authorized to access these systems. Once inside, he did not just poke around. He reportedly pulled personal information tied to real people and, in several cases, posted it to an Instagram account with the handle @ihackthegovernment.
The posts were not subtle, either. They were designed to show off access, humiliate victims, and prove he had the keys to government networks.
That kind of public exposure is what makes this case especially alarming. Plenty of breaches involve data theft, but broadcasting it on social media adds a second layer of harm. It turns private information into content, gives it a wider audience, and makes the damage far harder to contain.
Court filing reveals more victims and agencies
The newly filed court document describes three key victims, each connected to a different government related system. In addition to the Supreme Court filing platform, Moore allegedly accessed networks tied to AmeriCorps and the Department of Veterans Affairs.
AmeriCorps, known for its volunteer and stipend programs, was one of the targets where the personal fallout appears especially severe. According to the filing, Moore claimed access to AmeriCorps servers and published detailed personal information about a victim identified as SM.
The information listed includes the victim’s name, date of birth, email address, home address, phone number, citizenship status, veteran status, service history, and the last four digits of a Social Security number.
That is a dense bundle of identity data, and it is the exact type of mix that can be abused in everything from phishing and impersonation to account takeovers and financial fraud. Even the partial Social Security detail can be useful when combined with other personal identifiers, particularly if a criminal is trying to pass security checks or build a believable profile.
For the Supreme Court related victim, identified as GS, Moore allegedly posted the person’s name along with both current and past electronic filing records. While those filing records may not always contain the most sensitive personal data on their own, the exposure still raises serious questions about privacy and trust.
People working in and around the legal system rely on controlled access and predictable security boundaries. A breach that spills filing history into public view is the kind of incident that can rattle confidence across the board.
Veterans health information was also exposed
The most disturbing allegation involves the Department of Veterans Affairs. In that case, a victim identified as HW had identifiable health information exposed. The filing says Moore sent an associate a screenshot from HW’s MyHealtheVet account that identified the victim and showed medications that had been prescribed.
Health information is not just personal. It can be deeply sensitive, potentially stigmatizing, and difficult to erase once it spreads. Even when a screenshot is shared privately rather than posted widely, the act still represents a major breach of trust and privacy. It also highlights how easily a single compromised login can open the door to information that should be protected with the highest level of care.
The broader picture painted by the filing is not one of a one off mistake. It reads more like a repeatable playbook. Steal credentials, log in as a real user, pull personal data, then use social media to brag and prove the intrusion.
What happens next and why it matters
According to the court document, Moore faces a maximum sentence of one year in prison and a maximum fine of $100,000.
The penalties may sound modest compared to the scale of harm these incidents can cause, especially when personal and health information is involved. But the legal outcome will likely depend on the exact charges, the scope prosecutors can prove, and how the court weighs intent and impact.
This case is also a sharp reminder of how fragile credential based security can be. The alleged intrusions did not require Hollywood style hacking tricks. They relied on stolen usernames and passwords, which remain one of the most common entry points into high value systems.
Once an attacker has valid credentials, they can often blend in, move quickly, and access data without triggering immediate alarms.
And when attackers choose to publicize what they steal, the goal shifts from access to attention. That is when a breach becomes not just a security event, but a spectacle.
Follow TechBSB For More Updates